

The Mifare 1k Card is a popular contactless smart card used globally. These cards operate using RFID technology. They enable secure data exchange without physical contact. The Mifare 1k Card can store up to 1 kilobyte of data. This small size plays a crucial role in various applications.
In everyday life, we see these cards used for access control, public transportation, and event ticketing. Their convenience is undeniable. Security, however, is a concern. While the Mifare 1k Card offers encryption, vulnerabilities exist. Hackers can exploit weaknesses, leading to unauthorized access.
Understanding the Mifare 1k Card's functionality brings us closer to its potential risks. This card exemplifies both innovation and the need for caution. Clear awareness of its capabilities ensures better security measures can be taken. Users must remain vigilant.

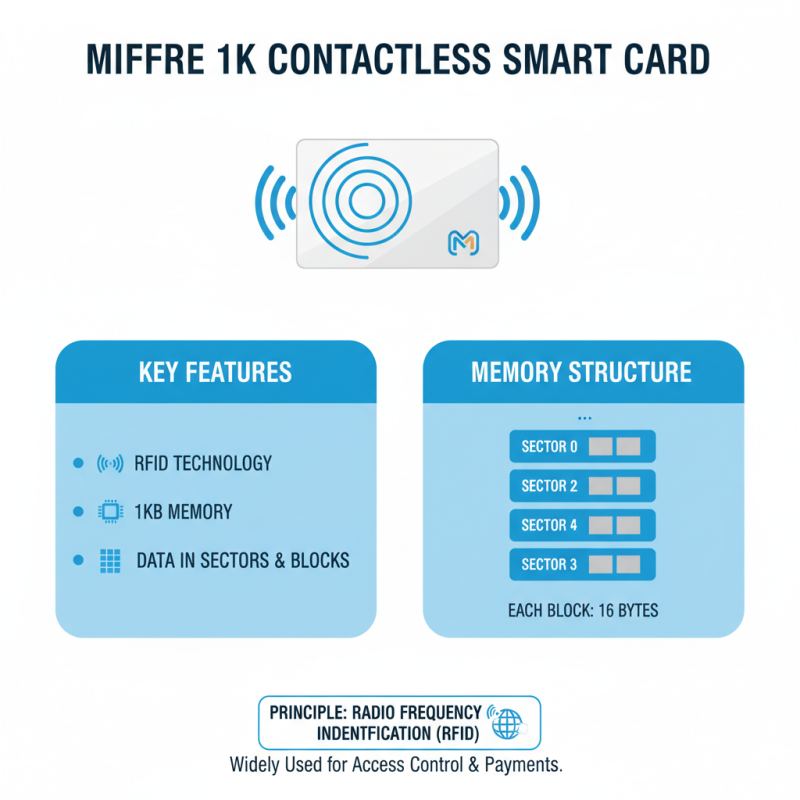
The Mifare 1k card is a widely used contactless smart card. It operates on the principle of radio frequency identification (RFID). This card stores data in a memory structure divided into sectors and blocks. Each block can hold 16 bytes of information.
A Mifare 1k card contains 1 kilobyte of memory. This allows for various applications, such as access control and public transport. When a card approaches a reader, the card and reader communicate through electromagnetic waves. The information transfer occurs rapidly, enabling quick transactions.
Despite its popularity, the Mifare 1k card has some limitations. Security features may not be adequate for very sensitive data. Users often overlook how easily data can be read by unauthorized readers. While the card is convenient, it raises questions about data safety and privacy. Awareness of these issues is crucial for effective use.
The Mifare 1k card is a type of
contactless smart card commonly used for
identification and access control. It contains
1 kilobyte of memory. This memory is organized into
16 sectors, with each sector containing
4 blocks. Each block can store
16 bytes of data. This structure allows it to effectively
manage various applications and information.
The card’s main components include an antenna, a
chip, and the memory itself. The antenna enables
wireless communication. It works with
RFID technology, providing contactless data transfer.
The chip processes data and manages commands sent from readers. Each sector has its own key
for security, making unauthorized access difficult. Reports indicate that the demand for
contactless cards will rise by over
30% by 2025. This indicates a
growing reliance on Mifare technology.
Tips: Always protect the card from
physical damage. Keep it away from strong
magnetic fields. These can disrupt its functioning. Ensure that the card reader is
compatible for optimal performance. Revisit the card’s settings periodically to maintain
security. Regular checks help in avoiding errors or data loss.
The Mifare 1k card is a popular contactless smart card used for various applications. It operates on principles of radio frequency identification (RFID). This card has a memory capacity of 1 kilobyte, divided into sectors for data storage. The communication process is quite intriguing.
When a reader gets near the Mifare 1k card, an electromagnetic field is created. This field powers the card when it enters the vicinity. The card then sends its unique identifier back to the reader. This exchange happens through a low-frequency signal. The communication protocol has always received attention and some criticism for its security aspects.
Data can be written and read from the card’s memory, but care is necessary. Misconfigurations can lead to vulnerabilities. Users often overlook the importance of secure coding during implementation. It’s not just about reading data; it’s about the security framework in place. Many projects have found issues that need addressing before launching in sensitive environments. Overall, understanding how Mifare 1k communication works reveals aspects that may require further thought and refinement.
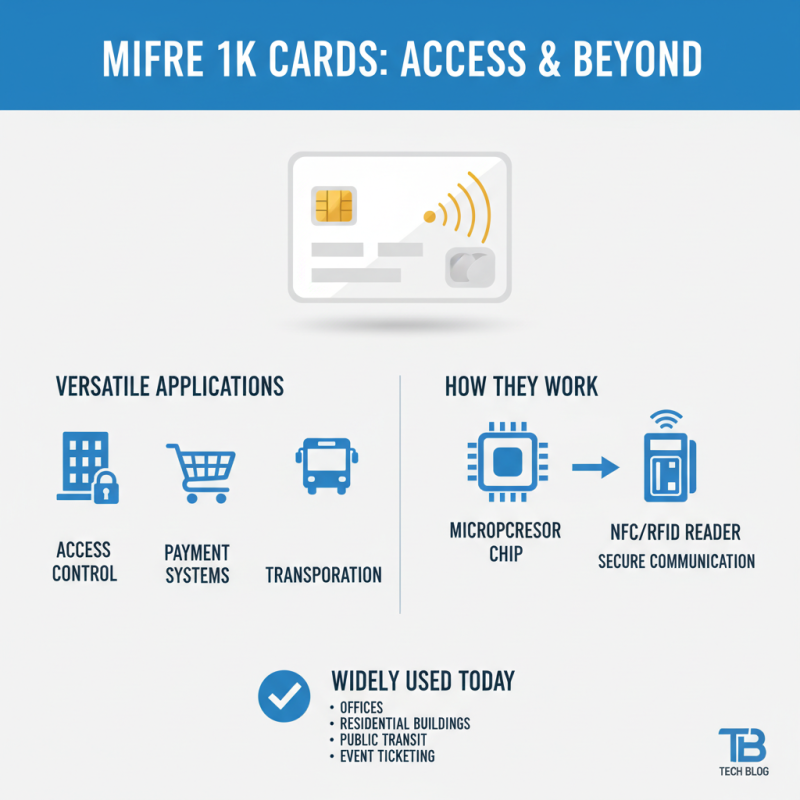
Mifare 1k cards are widely used in various applications today. They are particularly popular in access control systems. Many offices and buildings rely on these cards for secure entry. The cards contain a microprocessor that communicates with card readers. This interaction allows for efficient and secure access management.
In transportation, Mifare 1k cards are used for fare collection. Commuters can easily tap their cards at the turnstiles. This method speeds up the boarding process and reduces long lines. Some universities use these cards for student identification and library access. Students can check out books and access campus facilities with ease.
Despite their benefits, reliance on Mifare 1k cards raises concerns. What happens if a card is lost or stolen? Users may face challenges in obtaining replacements. Additionally, security concerns regarding data exposure cannot be ignored. Improving the technology could help mitigate these issues. Exploring better encryption methods is essential for enhancing user trust.
Mifare 1k cards are widely used in access control systems. They offer basic security features but have notable limitations. These cards store data using a 1KB memory structure, divided into 16 sectors. Each sector has its own access conditions, allowing for different levels of data protection. However, their simplicity also makes them vulnerable.
Research from the International Journal of Security and Networks indicates that the encryption used in Mifare 1k cards can be broken. The card employs a weak key encryption method, rendering it susceptible to attacks. In fact, nearly 60% of systems using Mifare 1k cards are at risk of unauthorized access due to these vulnerabilities. The lack of advanced security features raises concerns in high-security environments.
Despite their limitations, Mifare 1k cards remain popular due to their cost-effectiveness. Many organizations still rely on them for day-to-day operations. However, transitioning to more secure alternatives is crucial. Organizations should consider the implications of data breaches. Ignoring these threats can lead to significant financial and reputational damage. It’s clear that a reevaluation of security measures is needed.








